March 18, 2026
The problem with traditional passwords
Password problems persist despite decades of guidance and enforcement. This article examines traditional password issues at scale and evaluates secure, practical alternatives for enterprises.
Traditional passwords have dominated digital authentication for decades. From logging into a laptop to accessing cloud services, most systems still rely on users to create and manage passwords. Yet the widespread password problems users experience illustrate a fundamental disconnect between human behavior, threat landscapes, and secure access management. For individuals and organizations alike, traditional passwords are increasingly ineffective, costly, and a driver of both security risk and operational burden.
This article analyzes traditional password issues across consumer and enterprise contexts. It explores why passwords persist, the password issue at scale, and the alternatives organizations can adopt. It also considers concerns related to newer approaches like biometric authentication. Finally, it outlines the benefits and challenges of moving beyond passwords and reinforces why credential management must evolve.
Why traditional passwords persist
Despite the many data breaches caused by compromised credentials, the majority of online systems still require users to authenticate with a password. Many institutions publish best practices for strong password security and management precisely because users struggle with passwords at scale.
Reasons why passwords remain entrenched include:
- Ubiquity and simplicity of implementation: Password fields are basic features in authentication frameworks. They require no specialized hardware or device support.
- Backward compatibility: Legacy systems and applications often lack support for modern authentication standards, leading organizations to retain passwords for continuity.
- User familiarity: People understand the concept of a secret word or phrase even if they struggle to create secure ones.
- Regulatory guidance: Many compliance frameworks still include passwords as an acceptable factor, albeit with complexity or change requirements.
Despite all these reasons, it must be acknowledged that the persistence of passwords masks deeper structural weaknesses.
Widespread problems with traditional passwords
At the individual level, password problems manifest in predictable patterns that undermine both security and usability. The most common issues include:
1. Difficulty creating and remembering unique passwords
Users are asked to generate unique passwords for each system — work accounts, banking, social media, personal devices, utilities, and more. Few people can memorize dozens of unique passwords. When systems require complex rules, cognitive load increases, often leading to user frustration.
2. Reuse of passwords across systems
Because remembering a long list of complex passwords is difficult, users often reuse the same password across multiple accounts. If one service is breached, the credentials can be used to access others, a phenomenon known as credential stuffing.
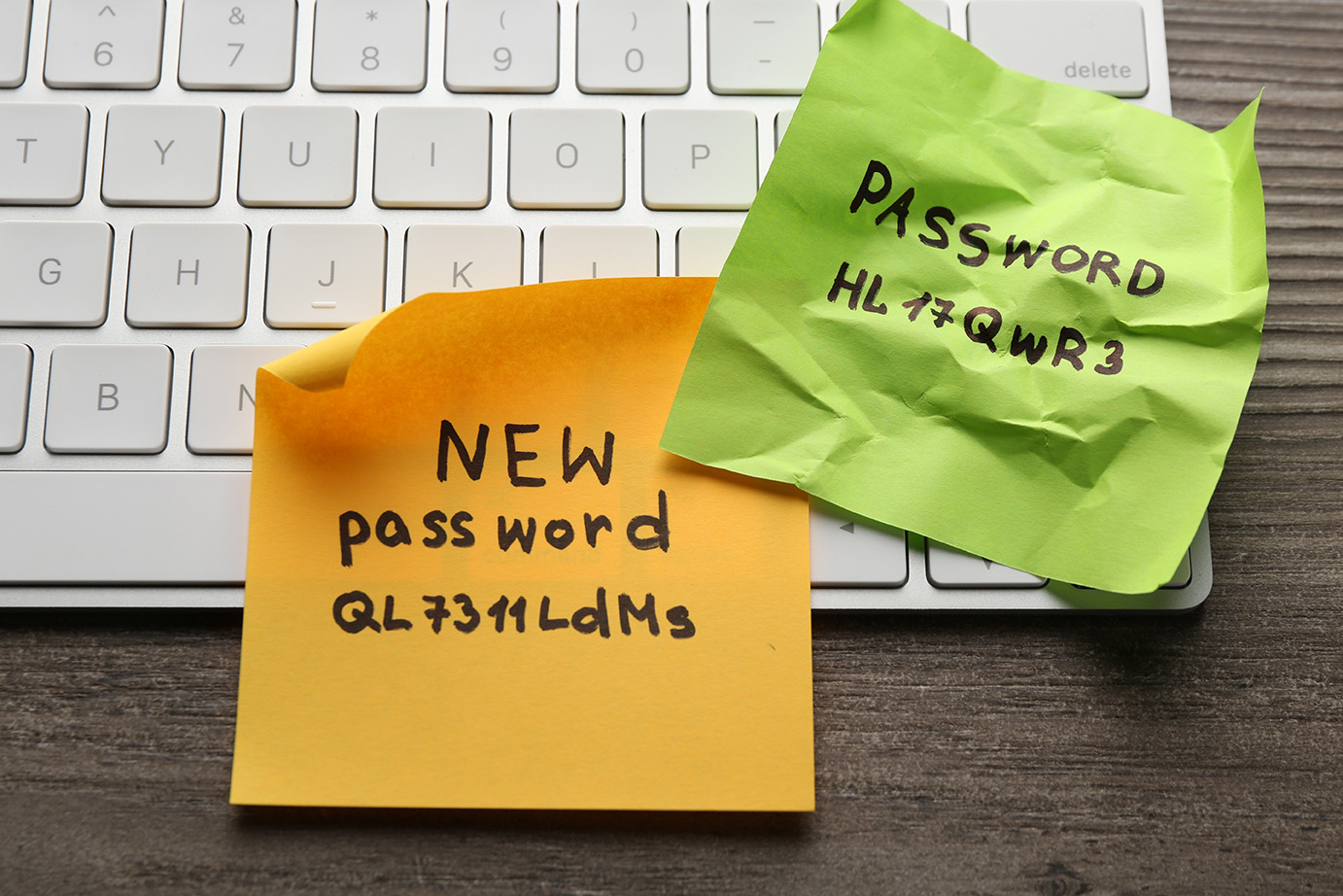
3. Writing down or storing passwords insecurely
To cope with forgetfulness, many users write their passwords on paper or sticky notes or save them in unencrypted local files. These fall outside enterprise control and create data leak risks.
4. Use of weak or easy-to-guess passwords
When forced to remember multiple unique logins, people often ignore strong password guidelines and create simple passwords (e.g., “123456”, pet names, birthdays) that can be guessed by attackers using brute force or social engineering attacks.
5. Lost passwords and help desk costs
Forgetting passwords triggers password resets. Help desks spend a great deal of time verifying identities and resetting accounts, especially in larger organizations where daily resets can number in the hundreds. The operational costs are non-trivial and erode productivity.
6. Password fatigue
Frequent password expiration policies limit the consequences of compromised credentials but also exacerbate password problems by forcing users to create new passwords regularly, increasing the likelihood they will forget or improperly store them.
Traditional password issues degrade the user experience and weaken overall security.
Enterprise impact of password problems
At the organizational level, password problems become magnified. Enterprises manage thousands to millions of identities across internal systems, cloud services, remote access, and endpoint devices. At this scale, password issues affect security teams, IT operations, and compliance frameworks.
1. Security risk and attack surface
Passwords are often the first — and weakest — layer of defense. They remain vulnerable to:
- Phishing: Attackers trick users into revealing passwords
- Credential stuffing: Automated use of compromised credentials across services
- Brute force attacks: Systems without rate limiting can be systematically probed until a password is guessed
- Replay attacks: Intercepted credentials can be reused without additional factors
Weak credentials at any point in the network can be leveraged to escalate access.
2. Credential management overhead
Enterprises must manage:
- Password rotation policies
- Enforcement of complexity rules
- Lockout policies to prevent brute force attacks
- Integration with identity directories and single sign-on (SSO) platforms
Each adds complexity and administrative overhead. Legacy systems that lack modern authentication APIs may require custom solutions, increasing cost.
3. IT support burden
Help desks spend large portions of their time handling password resets and account unlocks. This is a recurring operational cost directly tied to lost passwords and forgotten credentials.
4. Compliance and audit challenges
To satisfy regulatory requirements such as HIPAA, many organizations must regularly demonstrate effective credential management. Managing password policies across heterogeneous systems is difficult, and missing controls can lead to compliance gaps.
5. Remote work and endpoint access
With remote and hybrid work, systems that accept something besides a password — such as multifactor authentication (MFA) or token-based access — become critical. Traditional passwords alone are no longer sufficient to protect access from unmanaged or remote endpoints.
What else can I use besides a password?
Organizations and individuals across the globe are eager to explore how to log in without a password. Modern authentication frameworks offer alternatives that mitigate the drawbacks of traditional passwords. These include:
Passwordless approaches
Passwordless authentication allows users to access systems without entering a text password. Methods include:
- Biometric authentication: Fingerprint, facial recognition, or iris scans
- Device-based authentication: Using a trusted device (such as a smartphone or hardware token) as the authentication factor
- Passkeys: Cryptographic credentials stored in secure elements on devices that replace passwords in protocols such as FIDO2/WebAuthn
- Entry tokens: Time-based or challenge-response tokens delivered via secure channels
Biometric authentication
Biometric data uses unique physical characteristics to authenticate users. This convenient approach ties identity to a physical person rather than a memorized secret. However, biometric adoption raises valid privacy concerns.
Privacy concerns with biometrics
Some users are protective of their biometric identifiers because:
- Biometrics are immutable (you cannot change your fingerprint)
- They fear misuse or unauthorized sharing
- They worry that centralized storage could be compromised
These concerns are legitimate. Robust privacy protections require:
- On-device storage of biometric data rather than centralized servers
- Encryption and secure enclaves to ensure data cannot be extracted
- Clear privacy policies and compliance with data protection regulations
Quality biometric authentication architectures apply these protections to reduce exposure while strengthening authentication assurance.
Device as password
Modern authentication frameworks allow a registered device, such as a phone or laptop, to serve as the authentication factor. Examples include a smartphone that can generate cryptographic assertions after user presence is confirmed, and smartcards or hardware tokens that provide strong, phishing-resistant access.
Using a phone as a password leverages secure device-bound cryptographic credentials and user presence validation. When integrated into a unified access platform, device-based authentication supports phishing-resistant login flows without relying on memorized secrets.
Passkeys
Passkeys replace traditional passwords with cryptographic key pairs. When a user registers a device with a service, a private key remains on the device, while the service stores the public key. At login, the service sends a challenge that the device signs using the private key. This approach is:
- Resistant to phishing
- Resistant to replay attacks
- Not reliant on user memory
Passkeys represent a strong alternative to traditional passwords. Passkeys are already supported across major browsers and operating systems, and are being deployed at scale.
Multifactor authentication (MFA)
Even when passwords are still used, adding MFA significantly increases security. MFA combines something the user knows (password), with something they have (a phone or token), or something they are (biometric).
MFA mitigates risk because an attacker must compromise multiple factors, not just a reused or weak password.
For enterprises seeking intermediate steps toward passwordless authentication, MFA is a practical and widely adopted option.

Challenges in adopting password alternatives
Moving beyond passwords into passwordless authentication is not without challenges.
Legacy system integration
Many enterprise systems were designed with passwords in mind. Retrofitting these systems to accept something besides a password can require:
- Middleware or authentication gateways
- Custom development
- Phased rollouts to avoid disruption
User education and change management
Users are accustomed to entering passwords. Transitioning to a device-centric or biometric workflow requires:
- Communication on how alternatives work
- Support for initial enrollment
- Guidance on recovery when devices are lost
Privacy and trust
As noted, some users resist biometric approaches. Organizations must provide transparent privacy controls and options that respect user choice while maintaining security.
Device loss and account recovery
When using a phone as a password becomes the norm, enterprises need robust fallback and recovery options in case devices are lost or stolen. This includes:
- Secondary authentication factors
- Secure account recovery processes
- Device revocation mechanisms
Effective password management for enterprise organizations
To manage authentication risks during the transition away from passwords, organizations should implement strong password management for enterprise organizations. Best practices include:
- Centralized identity directories with policy enforcement
- SSO to reduce the number of authentication prompts
- MFA across privileged access
- Monitoring and analytics to detect anomalous login attempts
- Employee training on phishing and credential hygiene
These practices ease the burden of passwords while preparing the organization for alternate authentication models.
Passwordless at scale: The future of credential management
Enterprise authentication is moving toward credential management that reduces reliance on passwords. As organizations evaluate password alternatives, they often consider frameworks such as:
- FIDO2/WebAuthn for passkey and device-based authentication
- Adaptive authentication that adjusts based on risk context
- Biometric confirmation in secure, privacy-respecting architectures
The external documentation on passwordless authentication demonstrates growing interest in reducing password reliance and strengthening access controls. However, this transition requires strategic planning, integration effort, and careful attention to both usability and privacy.
Moving beyond traditional passwords
Traditional passwords alone are increasingly insufficient to meet modern enterprise security and usability requirements, particularly in high-risk or high-volume environments. Persistent password problems like forgotten credentials, password reuse, help-desk costs, and security vulnerabilities illustrate why organizations are exploring alternatives to traditional passwords.
Moving toward passwordless, MFA, device-centric, and biometric solutions can significantly reduce risk and operational cost. Yet successful adoption of advanced and passwordless access depends on thoughtful implementation, privacy protection, streamlined workflows, and effective integration with existing systems.
Enterprises that evolve their credential management strategies benefit from stronger security postures, reduced help desk overhead, and a strong foundation for future authentication standards — all while respecting user privacy and choice.
Explore how modern authentication strategies reduce password problems and strengthen credential management across your organization by requesting a demo today.

