Strengthen cybersecurity and simplify access with MFA and passwordless
Mitigate data leakage by requiring multiple verification methods, such as biometric authentication (facial recognition, fingerprint scanning), physical security keys, and secure PINs. Reduce the risk of unauthorized access. MFA also enhances identity management best practices and boosts user confidence in security measures.
Introducing Enterprise Access Management with Advanced and Passwordless Access
Smarter security, simpler access, and stronger insights
A comprehensive Enterprise Access Management (EAM) solution
Enterprise Access Management (EAM) offers simple, secure access control for endpoints and virtual desktops, single sign-on (SSO) to modern and legacy apps, passwordless and multifactor authentication, plus analytics and reporting.
EAM provides a comprehensive and user-friendly approach to secure access control for both physical endpoints and virtual desktop environments. It streamlines the process with SSO capabilities for both modern and legacy applications, ensuring seamless and secure user experiences. Additionally, the solution supports passwordless multi-factor authentication (MFA), enhancing security while reducing the burden of password management. To help organizations maintain robust security and optimize performance, EAM includes advanced analytics for monitoring and reporting. This versatile solution can be deployed as a standalone product or as part of a complete, integrated offering, catering to a wide range of organizational needs.
EAM with SSO enhances user convenience by allowing access to multiple applications with one set of credentials, reduces password fatigue, improves security by minimizing weak passwords, and lowers IT support costs by reducing password reset requests. SSO also streamlines the user experience, boosts productivity, and helps maintain compliance with security standards.
EAM with MFA adds an extra layer of security by requiring multiple forms of verification. It reduces the risk of unauthorized access, protects against password breaches, enhances user security, and complies with regulatory standards. MFA also improves user confidence and can simplify the login process by reducing the need to remember multiple passwords.
Improve cybersecurity with MFA that keeps users productive
Remove barriers to access across your organization and mitigate data leakage while supporting critical workflows and industry regulations like EPCS, CMMC, CJIS and more.

Benefits of choosing Imprivata for MFA
Ensure that clinicians and other frontline workers spend 80% less time accessing devices and apps to focus on critical tasks in a secure way with badge tap access, SSO, and more.
Reduce helpdesk calls for password issues, streamline access controls, improve user adoption of new applications.
Enforce security policies and compliance with multifactor authentication.
See how to access workstations with Face recognition
Set your passwordless strategy

Understanding passwordless
Gain a foundational understanding of passwordless authentication.

Practical advice for a journey to passwordless
Discover how passwordless authentication can remove friction for clinicians and drastically improve security posture for healthcare organizations.

The journey to passwordless for healthcare
A deep-dive analysis to provide CIOs and CISOs a balanced perspective on the pivotal aspects of passwordless.

Journey to passwordless: Paving the way for secure healthcare
Get insights into the passwordless maturity model and delve into how Imprivata’s solutions can facilitate the shift to passwordless.
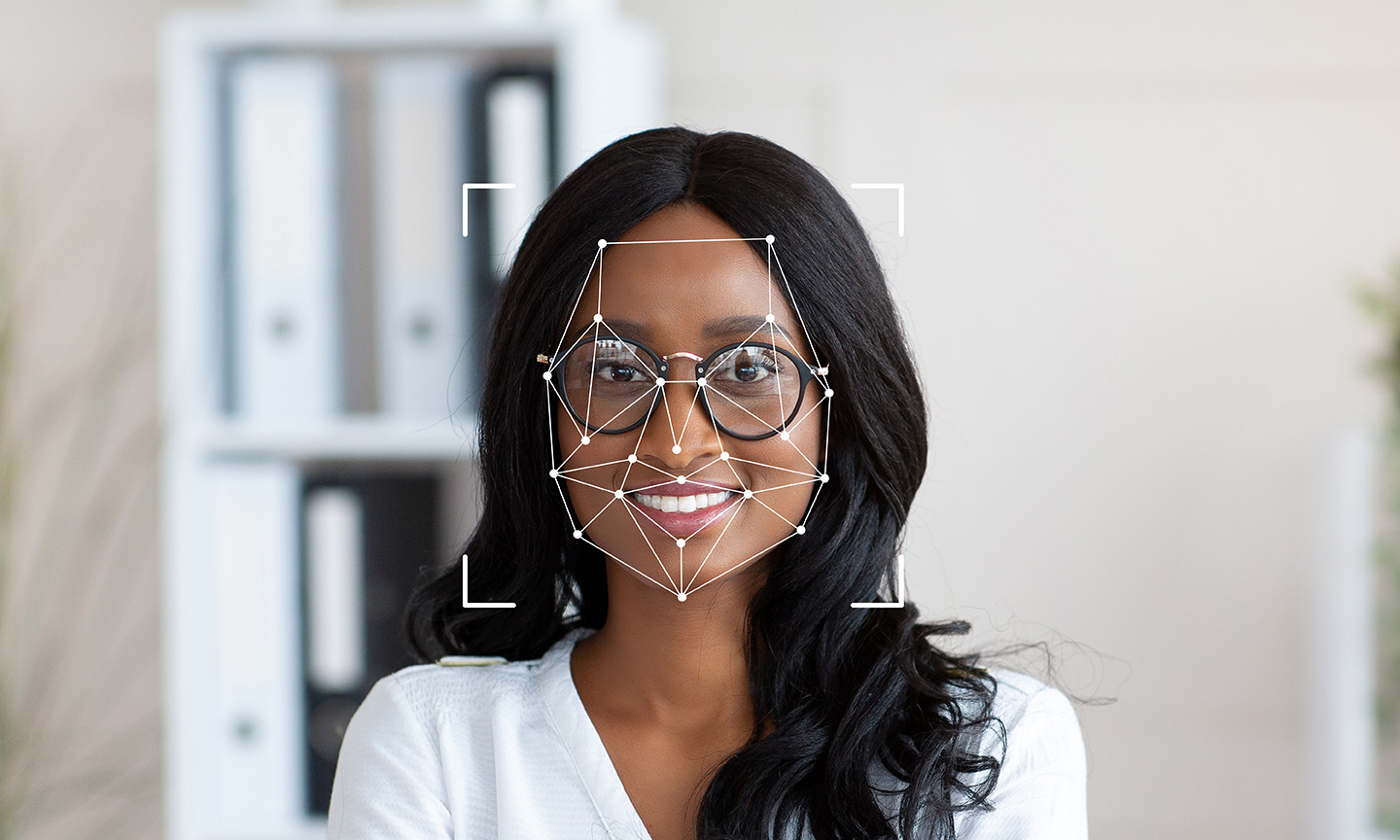
Imprivata face authentication
Get the details on this modern access solution built with privacy, security, and scalability in mind.
Imprivata adheres to high security standards.
Imprivata's software, certified for FIDO, EPCS, and ISO 27701, ensures robust passwordless authentication, compliance with DEA regulations, and enhanced privacy management, providing a secure and streamlined user experience. Learn more