November 16, 2020
Key Attributes and Habits of Privacy and Data Protection Program Maturity
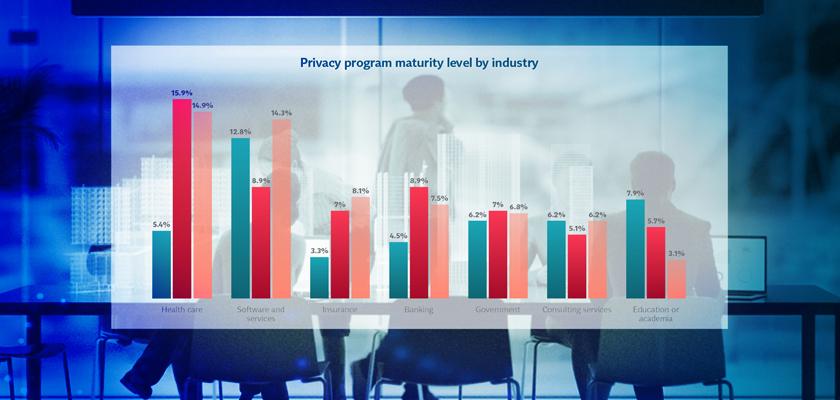
With increased consumer demand and global privacy regulations, corporate privacy and data protection programs are necessary now more than ever. But the sophistication and maturity of such programs vary dramatically from organization to organization, with some privacy programs in the rudimentary stages and others in the world-class category. And, according to the new research report, The Benefits, Attributes and Habits of Mature Data Privacy and Protection Programs, published by The International Association of Privacy Professionals (IAPP) and Imprivata FairWarning, organizations with data protection programs in the advanced stage of maturity have an advantage over their peers with programs in the early or middle stages.
Typical attributes and habits of mature privacy and data protection programs
In comparing those in the advanced stages of program maturity with those in the early stages, the research found that companies with advanced stage privacy and data protection programs possess different attributes and habits than their counterparts. Organizations with privacy and data protection programs in the advanced stage of maturity:
- Have a distinct privacy team (61.5%)
- Dedicate more employees to their privacy program (three, on average)
- Are more likely to have a Chief Information Security Officer or Chief Privacy Officer (75.5% and 72.3%, respectively)
- Are funded through a discrete budget or compliance program (41% and 34.2%, respectively)
- Report on the performance of their privacy program to their board (82%)
In addition to those mentioned above, most privacy and data protection programs in the advanced stage of maturity also have an incident response plan in place (95%) and regularly review and update data protection policies and procedures (96.9%). Furthermore, 82% of advanced-stage maturity programs know where most or all of their personally identifiable information and personal health information is located and where it flows within and outside their environment. Knowing this is critical for understanding data access trends and monitoring user activity to meet compliance requirements and maintain data privacy.
Organizations with mature programs also understand the data processing activities that impact the privacy and security of their data (96.3%). For example, suppose a hospital shares patient data with an HMO. In that case, they need to take extra precautions to ensure they’re only sharing data necessary for completing insurance claims and meeting privacy requirements outlined in HIPAA.
How data monitoring practices affect privacy program maturity
Many regulations require organizations to monitor user activity to support data discovery, because data governance starts with knowing your data and who has accessed it. In terms of user data monitoring practices, organizations in the advanced stages of maturity monitor user activity in applications that process personal data at much higher levels than those in the early stages. In fact, mature privacy programs use automated tools at twice the rate of those in the early stages of development. In comparison, only 28% of privacy programs in the early stages of maturity use automated tools to monitor user activity. Using an automated monitoring tool benefits organizations by:
- Saving time and eliminating manual efforts
- Detecting potential threat activity
- Mitigating the risk of human error
- Tracing data access for privacy requests
- Streamlining forensic investigations
- Increasing scalability of privacy and data protection efforts
Less-mature programs are stuck manually reviewing user activity logs (24%) or simply don’t monitor user activity at all (47.9%). If you’re looking to progress your organization’s privacy program maturity, look to automated monitoring tools like Imprivata FairWarning to track user activity, detect abnormal behavior, and support data privacy and compliance.
Common practices and benefits of privacy programs
It’s not all differences, though. Across all program maturity levels, the study found common, shared practices, including:
- Training: More than 50% of all respondents stated they have a separate privacy training module from other data security training.
- Interaction: Companies in all stages of program maturity reported interacting regularly with departments such as legal, information security, compliance, and information technology.
- Impact: Respondents across maturity levels stated that “increased employee privacy awareness” has the most positive impact on their organization.
What’s most important for data privacy and protection efforts?
The overarching message of the study is clear – while privacy and data protection programs are still maturing, there is a great deal of value to be had from simply having a program in place, even if it’s not as developed as it could be. That said, the more mature a privacy program is, the greater the benefit.
Organizations with more mature privacy programs – those that regularly review privacy procedures and processes to ensure continual improvement and conduct reviews to assess the effectiveness of privacy controls – see greater gains in almost all areas surveyed. When asked what benefits they are experiencing from their existing privacy programs, organizations with mature privacy programs saw the most significant improvements in:
- Reducing privacy complaints
- Increasing operational efficiencies
- Mitigating data breaches
- Building consumer (or patient) trust
Dedicating resources to a privacy program yields greater awareness of privacy-related issues internally, leading to better outcomes externally.
How mature is your organization’s data protection and privacy program?

